How to Secure Your Wireless Home Network – Prevent Others From Stealing BandWidth
Setting up a wireless network connection at your home or office has it’s own advantages. Apart from your desktop or laptop, you can use mobile phones, iPod or other wireless devices to surf the internet. Another advantage of using a wireless network connection is the portability and ease of use – you can carry the laptop to your balcony or bedroom and surf the internet without having to worry about cables and wires.
But using an unsecured wireless network can be risky, due to the following reasons:
- Anyone with basic computer knowledge can get in the range of your wireless network and start browsing the web, download files and do malicious activities. This would increase your internet usage bills.
- When other people “infiltrate” your network, there is always a potential risk of getting hacked or cracked. The uninvited guests can get access to your network, copy the shared files or folders or cripple the network all together.
- Since more people are sharing the wireless connection, the speed of surfing will decrease.
What is Piggybacking?
Piggybacking refers to gaining access of a wireless Internet connection by bringing one’s own laptop computer within the range of another’s wireless connection, and using that service without the subscriber’s explicit permission.
Consider a simple scenario – you live in a multi storeyed building and your apartment is in the 3rd floor. Someone from the 2nd floor always connects to your wireless network and browses the web, downloads files and you have to pay for the extra usage bills.
Basic mechanism of Piggybacking
How to Detect If Anyone Else is Using Your Wireless Network
First, you should detect whether an outsider is secretly using your wireless network connection for surfing the internet. Following are the steps involved to detect unauthorized activity in your wireless network:
1. Open the settings page of your wireless Router by typing 192.168.1.1 in the browser address bar and enter the username and password (admin, in most of the cases). Go to “Device Status” and you will see a “DHCP clients” table as shown below:
DHCP clients table for LinkSys and D Link Routers
The DHCP clients table lists the IP address and MAC address of the computers using the wireless network connection. Take note of the IP address and MAC address of your computer.
The IP address and MAC address of all computers and mobile devices which are using your wireless network connection, will be listed in this table. Whenever in doubt, check the DHCP clients table for unauthorized devices trying to breach your home network. If the DHCP clients table consists of multiple tables, be rest assured someone else is using your wireless home network without your consent.
2. Download Airsnare, it’s a free utility for Windows which can check for unexpected DHCP requests and MAC addresses in your Wireless home network. The software will scan your Wireless network and list any unidentified MAC address as shown below:
Detect unauthorized users in your Network
When you are confirmed that someone else regularly uses your wireless internet connection, it’s time to secure your wireless home network and deny access to outsiders.
How to Secure your Wireless Network and Prevent Unauthorized Access
1. Set up a password in your Router:
In most of the cases, no password is assigned to the router which means anyone connected to the wireless network can access the router and change the settings. To assign a password in your Router, open your Routers settings page by typing 192.168.1.1 in the browser address bar and enter the username and password (admin/admin or admin/password in most of the cases). Once you are logged into the router, click the “Change Password” link and assign a strong and secured password.
Change Routers password
This will prevent other users from accessing your Router using common username and password combination’s.
2. Change the Network’s SSID name
SSID stands for the name of the wireless network connection and in most of the cases, it is predefined as “default”. You should change the network SSID from “default” to some other name so that intruders can’t guess the name of the network they are connecting to. Another advantage of choosing a different name for SSID is that you will always be sure that you are connected to your home network and not anyone else’s.
Change Network SSID in DSL router
To change the SSID name, log in to the router and go to Wireless > Basic and change the SSID name to something unique. (Tip: use something like “Virus or Trojan”, intruders may think twice before entering your network :) )
3. Switch to WPA Encrption from WEP
Wireless encryption can vary between WEP, WPA and WPA2 (latest). WEP is the least secure encyption type while WAP2 is the most secure encyption type for wireless signals.
To change your wireless network’s encryption type, log in to Router’s settings page and go to Wireless > Security. Choose the desired level of encryption type from the drop down menu as shown below:
Wireless encryption settings
Hit “Save” and reboot the router for the changes to take effect.
Note: If you are using old devices or computers with very old mother boards and processors, WPA encryption might not work.
4. Set up Mac Filters in your Router
Every computer, laptop or a mobile device has a unique MAC address, which can be used to identify the device connected in a network. You can add specific MAC addresses in your Router’s settings and configure the router to share the internet connection to only these MAC addresses.
To find the MAC address of your computer, open the command prompt and type ipconfig/all. You will find the MAC address of your computer under “Physical address” as shown below:
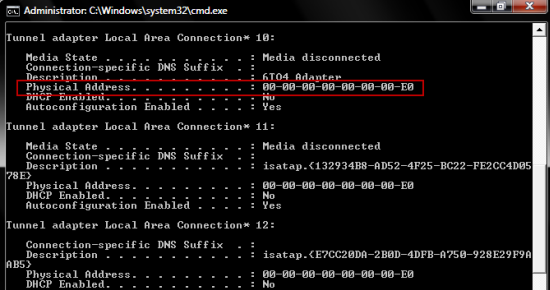
Find MAC address of your computer
Now open your Router’s settings page from the browser and go to Wireless > Mac filter. Add the above MAC address as a “New Filter” and reboot the Router for the changes to take effect.
Set MAC filters in your Router
Once you have added all the MAC filters of your computer, laptop, mobiles and other devices – your wireless network is quite secured. Anybody trying to access your home network will have to know your computer’s MAC address. While this isn’t impossible, but the intruders will have a tough time tweaking the settings.