Smartphone Security Risks You Are Not Aware About
It is difficult to understand why but users are not much aware about the security risks in their phones as compared to their awareness about their computers. In fact, smartphones are much more vulnerable to attacks than your standard home computer. Therefore it is advisable to go through this list of smartphone security risks issues and keep them in mind while using your smartphones from today.
SMS or App Phishing
Before the outbreak of smartphones, phishing attacks by hackers were limited to spamming through emails. But now the attacker has the ability to collect sensitive user details like names, addresses, bank account numbers, passwords and credit card numbers through just an app or a simple SMS message. These may actually seem legitimate at first glance and may fool many users. Such apps or messages take the user to links where they are asked to enter their sensitive details through a number of excuses which are be later used by them for hazardous purposes. For example, this may be done with the use of sms/email that tell you about a prize money or gift you have won out of thin air. Never ever heed to such messages. If something sounds too good to be true, it probably isn’t.
Spyware Attacks
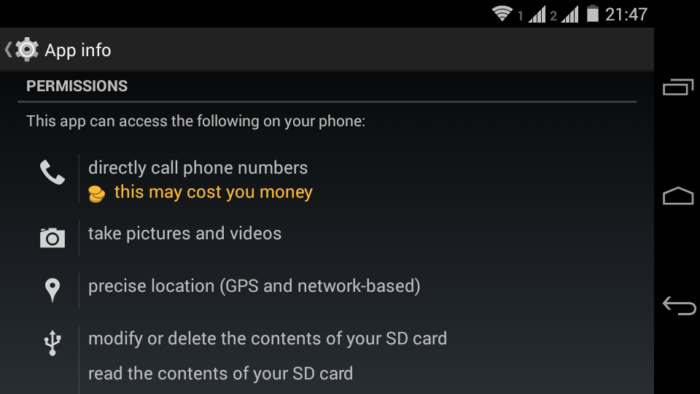
Like malware/spywares in your computers, your smartphone can also be infected with them. Spyware is a malicious program that keeps a close watch on the usage of the smartphone and collects and sends this private usage data to other clients for marketing purposes. They may be contacted through surfing unsafe websites or downloading objectionable apps. There are numerous apps on the app stores that ask for permissions while installation which they don’t even need to run. Such controversial permissions may range from asking to read emails and sms, access the contact book, determining the device location and much more. Such data is then used by for targeted advertisements by companies that pay these apps for such valuable information. Smartphones act as a powerhouse of data collection and therefore this makes them an attractive target for spyware attacks. Users should always check out the app permissions section while installing apps to be sure the apps are not asking permissions above those which they need to operate.
Network Spoofing Attacks
This kind of attack from hackers is conducted with the help of rouge wifi hotspots that are insecure and thus enable the attacker to sneak in and steal the user data while he is using the Internet through the network on websites which do not use Transport Layer Securities or SSL Certificates. This technique also facilitates to carry out phishing attacks easily by intercepting the user communication. Such attacks can be prevented by keeping tabs about whether the website is SSL certified and by using public wifis of only trusted sources. Untrusted sources like the free wifi of the neighbor and random public wifis which are not password protected, act as an active ground for hackers to covertly find careless users.
Surveillance attacks
Since most users keep their smartphones with them almost all the time, the smartphones can also be used for surveillance of target personalities especially famous people. The attacker may infect the target’s phone with spying tools even with the help of gaming applications. The user may easily trust such apps but a closer look might reveal the extent of the permissions the app demands are controversial. There kinds of spying apps take the user data and upload them to a remote server. Since the smartphones have multiple features like GPS locations, microphones, cameras, motion detector etc, such apps exploit these functions to the core. Therefore, users should do a background check for apps before installing them and also check about the permissions they demand.
Conclusion
If you think your smartphone addiction is the primary threat to your security, you can keep it under check with this app called Instant. Always be aware. You should never just download any app without proof reading about its security issues. Be responsible and be safe.